Latest Research
Latest Research & Infographics
Projects
CLICK ON ICON TO SEE PROJECT COMPONENT
Delivering Reliable NG9-1-1 Capabilities
Nearly all Americans today are using cell phones, with a growing number of U.S. households relying solely on mobile devices for communication. Yet most citizens do not realize that existing 9-1-1 emergency systems do not handle mobile data accurately—location data from mobile phones can be inexact and text messages may not even reach traditional 9-1-1 call centers.
How quickly are local and state government entities adopting Next Generation 9-1-1 systems (NG9-1-1) to protect their citizenry? Are current updates enough?
To gauge government entities’ understanding of the needs associated with the changing emergency response system, General Dynamics Information Technology (GDIT) commissioned Market Connections to determine how far along state and local governments are in planning and implementing NG9-1-1 systems, as well as the challenges they face.
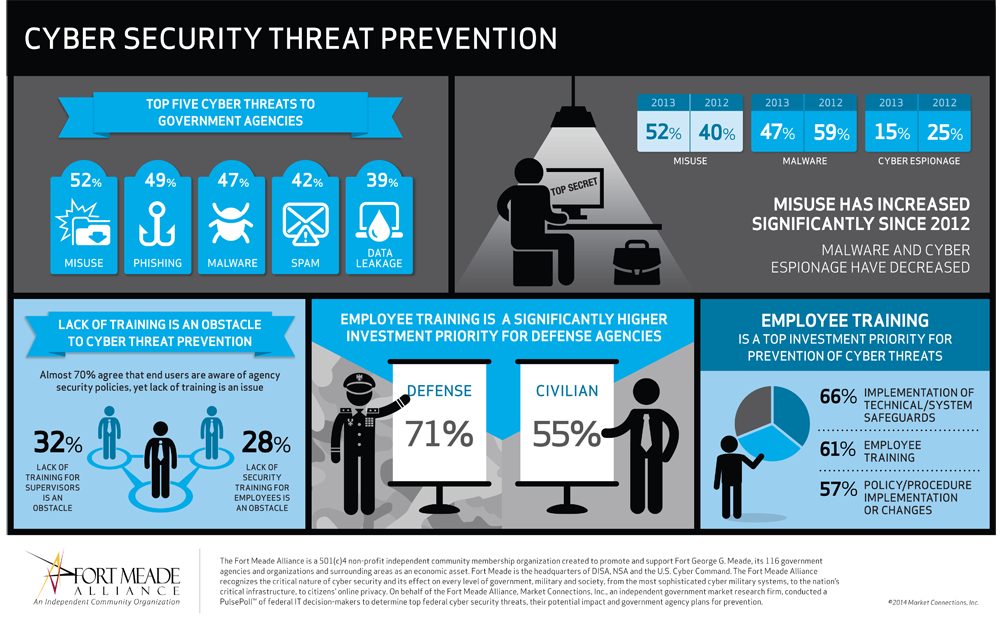
Cybersecurity Threat Prevention
Cybersecurity PulsePoll™ Identifies Training as Top Priority for Government
A Market Connections PulsePoll™ of government IT professionals, conducted on behalf of Fort Meade Alliance, finds that training to prevent cyber security threats is an investment priority for more than 60 percent of federal civilian and defense/military organizations. The research found that:
- Almost 70 percent of government IT decision-makers agree that end users are aware of agency security policies, yet lack of training is considered an obstacle to preventing cyber threats by about one-third of survey respondents.
- Employee training is among the top investment priorities for prevention of insider threats
- Employee training is a significantly higher investment priority for defense agencies, compared with their civilian counterparts
“Cyber security awareness training can help solve many of the challenges we face with protecting information technology assets, and our government’s most sensitive information and mission-critical systems,” said Deon Viergutz, president of Ft. Meade Alliance and director of cyber operations for Lockheed Martin Information Systems & Global Solutions.
“Through educational programs developed by our institutions of higher learning and through E.A.R.N., and other workforce training programs offered by the state of Maryland, current and future generations of cyber warriors are being prepared for careers in the industry,” said Jeffrey Wells, executive director of cyber development in the Maryland Department of Business and Economic Development. “With input from the government, this survey reinforces the need for education and training to evolve to meet the ever-growing demand for qualified workers in the field.”
The poll measured awareness and attitudes about a wide range of cyber security topics, including threats, challenges to insider threat prevention and investment priorities for prevention of insider threats. Survey results reflect respondents from federal civilian and defense/military agencies.

The State of Marketing and PR
Research Reveals Nine Marketing and PR Myths
A new Market Connections study, commissioned by Vocus, busts marketing and public relations (PR) myths and reveals how marketing automation is delivering benefits in terms of efficiency, analytics and campaign management.
The study shows a changing world of haves and have-nots for marketing professionals and a movement toward digital and social media in public relations. Vocus, a leading provider of cloud-based PR and marketing software, released the study in early June 2014 at their Demand Success conference.
The study, based on an online national survey of 325 mid- and senior-level marketing and PR professionals in May 2014, supports many current trends in marketing and PR, but busts several generally accepted myths on the social Internet. The research exposes the changes in both marketing and PR professionals’ worlds. In PR, it reveals a move towards digital and social media. In marketing, a struggle to grasp digital media technologies emerging in their space. Along with these notable shifts, it also shines light onto common myths upheld within the industries.
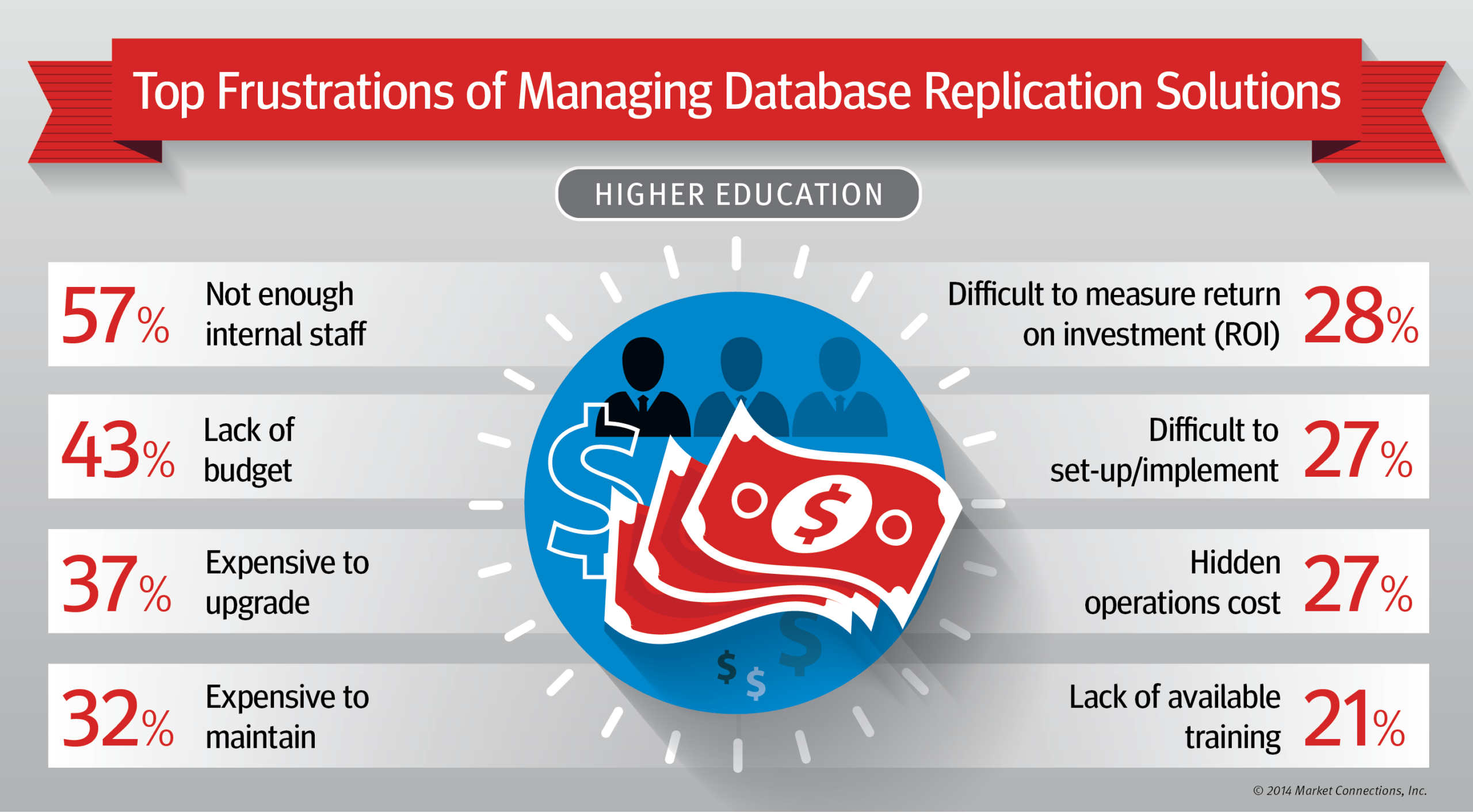
Data Replication and Integration Tools:
Reducing Risk & Improving Reliability for Higher Education Data
Accountability is the new mantra for higher education administrators, and it requires merging the institution’s intellectual identity, constituents, and business systems and services. The ability to leverage these assets is directly related to success and results in this pressing need for accountability.
Dell Software commissioned Market Connections to poll higher education IT administrators on awareness of, and attitudes toward, the use of data replication and integration tools, especially the features they deem most critical when selecting a tool.
Download a PDF of the white paper and infographics, which detail top frustrations and the most critical features of managing data and the supporting suite of tools.

Managing the Unpredictable Human Element of Cybersecurity
SolarWinds, a leading provider of powerful and affordable IT management software, commissioned Market Connections to conduct a cybersecurity study that revealed malicious insider and outsider threats affecting federal agencies, even though they feel cybersecurity-ready.
SolarWinds has used this research and associated report, white paper and infographics for some advanced thought leadership marketing strategies that include publicity, social media promotions, webinars, speaking engagements and demand generation.
The study found that many agencies are still confronted by threats from careless and untrained insiders, and are tasked with mastering IT security despite organizational and budget challenges.
SolarWinds generated significant exposure, more than 500 leads and an award for this strategic thought leadership promotion:
- Press coverage – 21 articles in key online and print trade media
- More than 1,250 views of the research report on Slideshare
- More than 1,200 views of the infographics on Slideshare and LinkedIn
- Overall Best in Show award at the June 2014 AFCEA Cyber Conference Solutions Trail for a presentation leveraging the research and insights
Governance, Risk & Compliance:
Consistency Keeps Agency Data Secure
POLL REVEALS HALF OF GOVERNMENT AGENCIES DO NOT ADDRESS NETWORK VULNERABILITIES PROACTIVELY
A new poll sponsored by Dell Software reveals half of government agencies do not address network vulnerabilities proactively, impacting security compliance and the ability to respond to threats.
With federal IT departments stretched thin, how many days has it been since you last verified meeting internal policies, backed up your data, or monitored your environment to see who has access to what and whether they’ve done anything with that access?
IF THE ANSWER IS MORE THAN ONE HOUR YOU MAY RUN THE RISK OF:
- Failing an audit
- Non-compliance with new mandates
- Inability to provide evidence of data to satisfy legal requests
- Inability to respond to a request from senior management, HR, or finance for a report
- A data breach threat
- Loss of critical data
When it comes to data security, it’s not a matter of IF something will go wrong, but WHEN. Is your agency prepared?
Fill out the form below to download the study results white paper, which details top federal IT compliance and governance concerns, potential costs of non-compliance and key attributes of audit and compliance solutions.
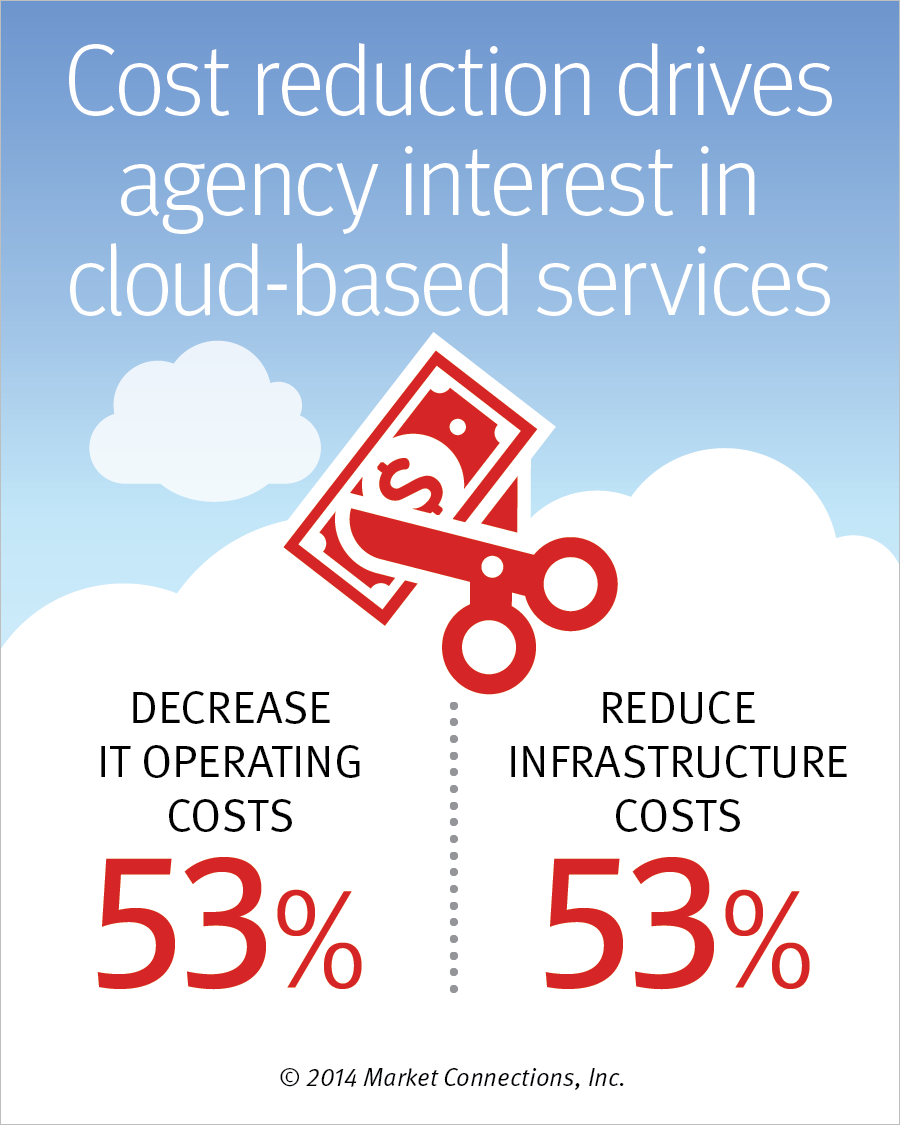
The Keys to Successful Cloud Migrations
New Research Guides Federal Agencies as they Move to the Cloud
It is not a matter of whether federal civilian agencies will move to the cloud. It’s a matter of when … and how. Choosing flexible solutions that address current and future needs are the keys to making the move cost-effective, secure and seamless.
This white paper from Market Connections and General Dynamics Information Technology outlines four keys to successful cloud migrations and includes detailed research findings, such as the status of federal migrations to the cloud, top benefits and government’s preferred cloud services models.
Fill out the form below to download the white paper, which addresses how to mitigate risks such as vendor lock-in, performance issues and unanticipated costs.
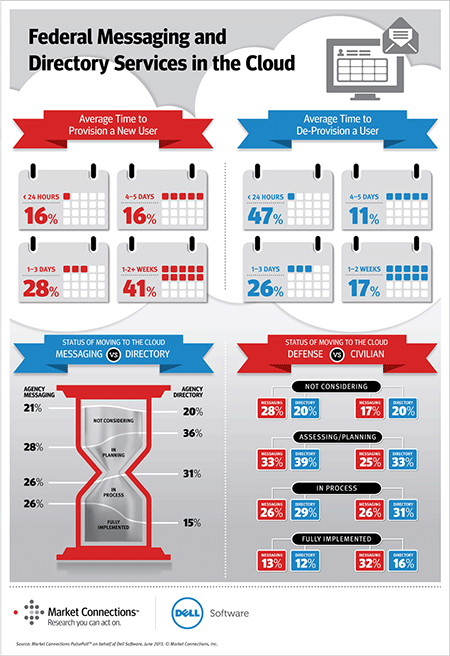
Federal Messaging and Directory Services in the Cloud
The slow provisioning and de-provisioning of government employees can be costing the federal government millions of dollars each year, which is a key finding of Market Connections PulsePollTM commissioned by Dell Software.
With the federal workforce totaling more than 4.4 million employees, users need instant access to technology to maintain productivity—starting the first day on the job. With federal government turnover of approximately 80,000 personnel per month, agencies’ ability to provision and de-provision users can have a tremendous impact on operational costs.
According to the poll of 200 federal IT decision-makers, agencies are slow to move messaging and directory services to the cloud, which can play a significant role in mitigating this problem. Almost half (41%) of respondents say their agency takes one week to more than two weeks to fully provision a user, while more than a quarter (28%) take four business days to two weeks.
KEY RESEARCH FINDINGS INCLUDE:
- 41 percent of respondents say their agency takes from one week to more than two weeks to fully provision new users.
- Every day of lost work costs nearly $200 per new hire, costing large agencies up to $20M a year.
- 54 percent of all agencies take more than a day for de-provisioning.
- 26 percent of respondents have moved messaging services and 15 percent have moved directory services to more efficient cloud environments.
- 61 percent of respondents believe their organizations are adequately staffed to de-provision users in less than 24 hours; however, more than half of all agencies take longer than one day to de-provision users.
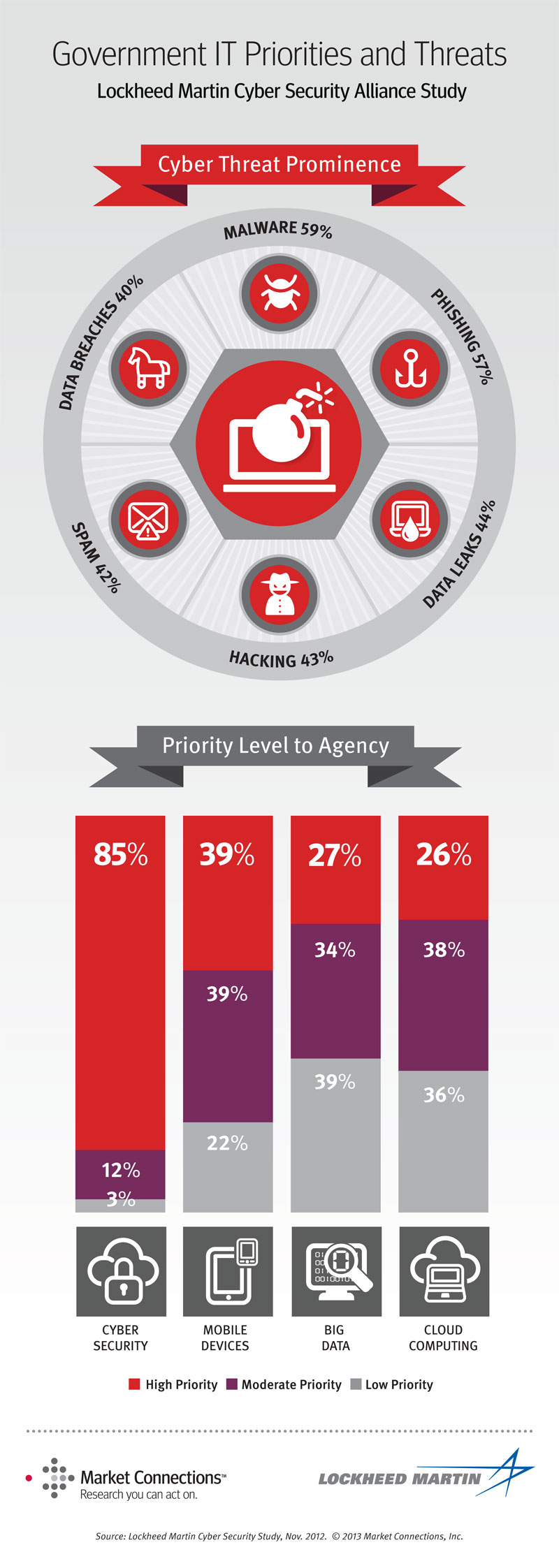
Cyber Security and Transformational Technologies
Keeping Systems and Data Safe
Lockheed Martin and its Cyber Security Alliance Partners recently commissioned Market Connections to conduct their third annual cyber security survey. The results, available in a new white paper titled “Cyber Security and Transformational Technologies – Keeping Systems and Data Safe,” show that 85% of government technology decision makers see cyber security as a high priority and currently have one or more major initiatives underway. The white paper describes and ranks the types of security threats agencies face and recommends preparedness strategies to effectively defend against these pressures. While most agencies consider themselves “well prepared” to deal with security threats, they continue to invest in other new technologies because mobile device initiatives, cloud computing and big data solutions contribute to more economical and affordable approaches to sharing and storing information when compared to traditional methods that require additional cyber security measures to ensure protection.
Awareness, Trust & Security to Shape Government Cloud Adoption
The Lockheed Martin Cyber Security Alliance and Market Connections presented the webinar Securing Data in the Cloud on June 23, 2010. The live event shared findings from a research study of federal government IT decision-makers and influencers involved specifically in cyber-related activities. The presentation detailed awareness of and attitudes on cloud computing and cyber security in federal agencies, in addition to considerations when moving to a cloud computing environment.
SPEAKERS INCLUDED:
- Melvin Greer, Lockheed Martin Information Systems and Global Solutions’ (IS&GS) Cloud Computing Strategist, moderated the session.
- Cynthia Poole, Director of Research Services and expert analyst at Market Connections, presented the results of the research study commissioned by the Lockheed Martin Cyber Security Alliance.
- John Pescatore, Gartner Vice President, Distinguished Analyst and Cyber Security expert, provided additional insights on security considerations and best practices for government agencies moving to a cloud computing environment.
More on the Lockheed Martin Cyber Security Alliance.
