Homepage Research Section
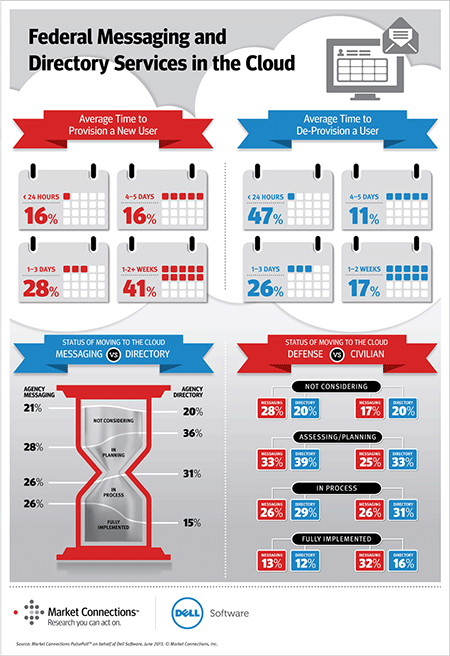
Federal Messaging and Directory Services in the Cloud
The slow provisioning and de-provisioning of government employees can be costing the federal government millions of dollars each year, which is a key finding of Market Connections PulsePollTM commissioned by Dell Software.
With the federal workforce totaling more than 4.4 million employees, users need instant access to technology to maintain productivity—starting the first day on the job. With federal government turnover of approximately 80,000 personnel per month, agencies’ ability to provision and de-provision users can have a tremendous impact on operational costs.
According to the poll of 200 federal IT decision-makers, agencies are slow to move messaging and directory services to the cloud, which can play a significant role in mitigating this problem. Almost half (41%) of respondents say their agency takes one week to more than two weeks to fully provision a user, while more than a quarter (28%) take four business days to two weeks.
KEY RESEARCH FINDINGS INCLUDE:
- 41 percent of respondents say their agency takes from one week to more than two weeks to fully provision new users.
- Every day of lost work costs nearly $200 per new hire, costing large agencies up to $20M a year.
- 54 percent of all agencies take more than a day for de-provisioning.
- 26 percent of respondents have moved messaging services and 15 percent have moved directory services to more efficient cloud environments.
- 61 percent of respondents believe their organizations are adequately staffed to de-provision users in less than 24 hours; however, more than half of all agencies take longer than one day to de-provision users.
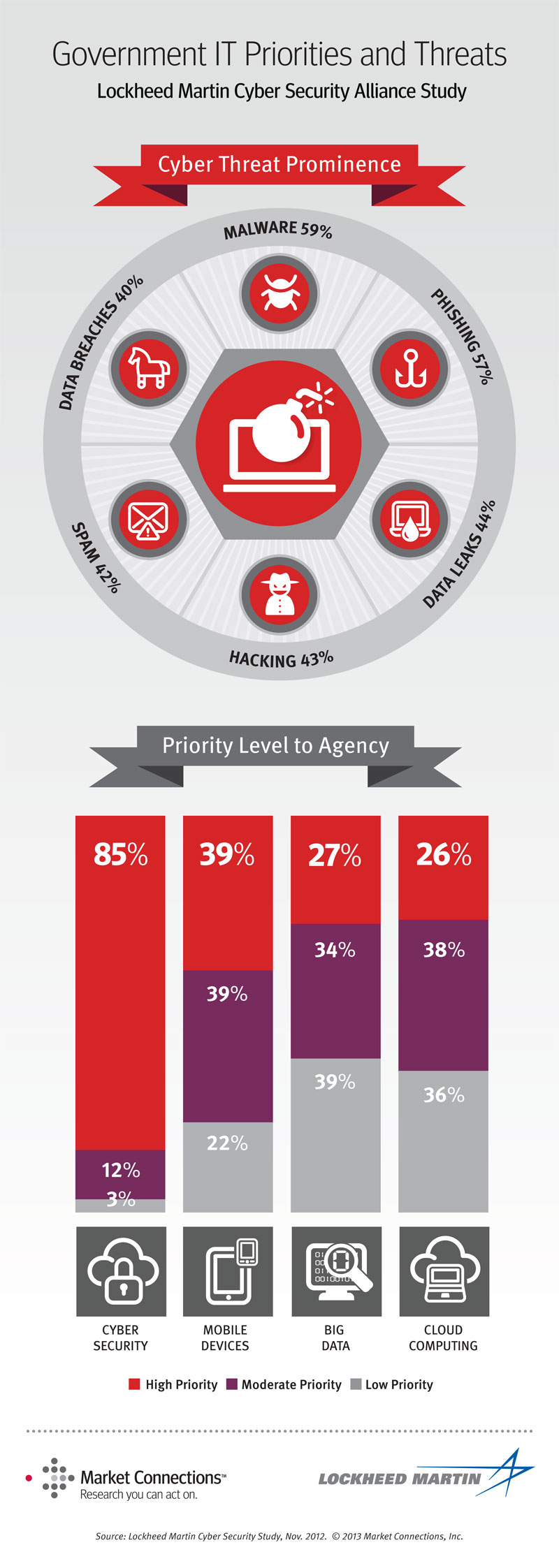
Cyber Security and Transformational Technologies
Keeping Systems and Data Safe
Lockheed Martin and its Cyber Security Alliance Partners recently commissioned Market Connections to conduct their third annual cyber security survey. The results, available in a new white paper titled “Cyber Security and Transformational Technologies – Keeping Systems and Data Safe,” show that 85% of government technology decision makers see cyber security as a high priority and currently have one or more major initiatives underway. The white paper describes and ranks the types of security threats agencies face and recommends preparedness strategies to effectively defend against these pressures. While most agencies consider themselves “well prepared” to deal with security threats, they continue to invest in other new technologies because mobile device initiatives, cloud computing and big data solutions contribute to more economical and affordable approaches to sharing and storing information when compared to traditional methods that require additional cyber security measures to ensure protection.
Awareness, Trust & Security to Shape Government Cloud Adoption
The Lockheed Martin Cyber Security Alliance and Market Connections presented the webinar Securing Data in the Cloud on June 23, 2010. The live event shared findings from a research study of federal government IT decision-makers and influencers involved specifically in cyber-related activities. The presentation detailed awareness of and attitudes on cloud computing and cyber security in federal agencies, in addition to considerations when moving to a cloud computing environment.
SPEAKERS INCLUDED:
- Melvin Greer, Lockheed Martin Information Systems and Global Solutions’ (IS&GS) Cloud Computing Strategist, moderated the session.
- Cynthia Poole, Director of Research Services and expert analyst at Market Connections, presented the results of the research study commissioned by the Lockheed Martin Cyber Security Alliance.
- John Pescatore, Gartner Vice President, Distinguished Analyst and Cyber Security expert, provided additional insights on security considerations and best practices for government agencies moving to a cloud computing environment.
More on the Lockheed Martin Cyber Security Alliance.
